How to Delete Absolute Secure Access
Published by NetMotion Software Inc. on 2023-10-30We have made it super easy to delete Absolute Secure Access account and/or app.
Table of Contents:
Guide to Delete Absolute Secure Access
Things to note before removing Absolute Secure Access:
- The developer of Absolute Secure Access is NetMotion Software Inc. and all inquiries must go to them.
- Check the Terms of Services and/or Privacy policy of NetMotion Software Inc. to know if they support self-serve account deletion:
- Under the GDPR, Residents of the European Union and United Kingdom have a "right to erasure" and can request any developer like NetMotion Software Inc. holding their data to delete it. The law mandates that NetMotion Software Inc. must comply within a month.
- American residents (California only - you can claim to reside here) are empowered by the CCPA to request that NetMotion Software Inc. delete any data it has on you or risk incurring a fine (upto 7.5k usd).
- If you have an active subscription, it is recommended you unsubscribe before deleting your account or the app.
How to delete Absolute Secure Access account:
Generally, here are your options if you need your account deleted:
Option 1: Reach out to Absolute Secure Access via Justuseapp. Get all Contact details →
Option 2: Visit the Absolute Secure Access website directly Here →
Option 3: Contact Absolute Secure Access Support/ Customer Service:
- 15% Contact Match
- Developer: NetMotion Software, Inc.
- E-Mail: [email protected]
- Website: Visit Absolute Secure Access Website
Option 4: Check Absolute Secure Access's Privacy/TOS/Support channels below for their Data-deletion/request policy then contact them:
*Pro-tip: Once you visit any of the links above, Use your browser "Find on page" to find "@". It immediately shows the neccessary emails.
How to Delete Absolute Secure Access from your iPhone or Android.
Delete Absolute Secure Access from iPhone.
To delete Absolute Secure Access from your iPhone, Follow these steps:
- On your homescreen, Tap and hold Absolute Secure Access until it starts shaking.
- Once it starts to shake, you'll see an X Mark at the top of the app icon.
- Click on that X to delete the Absolute Secure Access app from your phone.
Method 2:
Go to Settings and click on General then click on "iPhone Storage". You will then scroll down to see the list of all the apps installed on your iPhone. Tap on the app you want to uninstall and delete the app.
For iOS 11 and above:
Go into your Settings and click on "General" and then click on iPhone Storage. You will see the option "Offload Unused Apps". Right next to it is the "Enable" option. Click on the "Enable" option and this will offload the apps that you don't use.
Delete Absolute Secure Access from Android
- First open the Google Play app, then press the hamburger menu icon on the top left corner.
- After doing these, go to "My Apps and Games" option, then go to the "Installed" option.
- You'll see a list of all your installed apps on your phone.
- Now choose Absolute Secure Access, then click on "uninstall".
- Also you can specifically search for the app you want to uninstall by searching for that app in the search bar then select and uninstall.
Have a Problem with Absolute Secure Access? Report Issue
Leave a comment:
What is Absolute Secure Access?
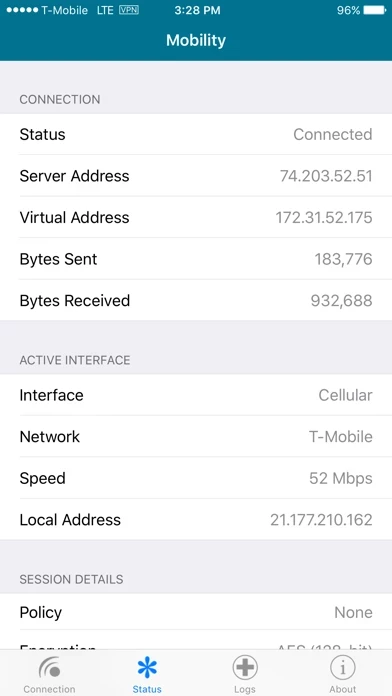
NETMOTION ZTNA PLATFORM NetMotion ZTNA analyzes every single request by remote workers, using dynamic, contextual data about each device to authorize access to enterprise resources. Unwanted and risky connections are blocked, keeping users safe from online threats and risky content – and crucially, outside of enterprise resources they are not approved to access. Using patented technologies, NetMotion makes networks more resilient and significantly reduces connectivity issues. With rich diagnostics data, IT teams can support remote workers as effectively as if they were seated in the office. • Real-time risk analysis of every access attempt, using 25+ different conditions • The ability to make applications go ‘dark’, protecting them from unapproved access • Dynamic web filtering for all remote workers, enforcing acceptable usage policy on a contextual basis. • Endpoint-based decision making, streamlining performance and improving the user experience. • An optimized tunnel to stabiliz...