How to Delete Tachyon VPN
Published by BlockStone LTD on 2023-02-07We have made it super easy to delete Tachyon VPN - Private Proxy account and/or app.
Table of Contents:
Guide to Delete Tachyon VPN - Private Proxy
Things to note before removing Tachyon VPN:
- The developer of Tachyon VPN is BlockStone LTD and all inquiries must go to them.
- Check the Terms of Services and/or Privacy policy of BlockStone LTD to know if they support self-serve account deletion:
- Under the GDPR, Residents of the European Union and United Kingdom have a "right to erasure" and can request any developer like BlockStone LTD holding their data to delete it. The law mandates that BlockStone LTD must comply within a month.
- American residents (California only - you can claim to reside here) are empowered by the CCPA to request that BlockStone LTD delete any data it has on you or risk incurring a fine (upto 7.5k usd).
- If you have an active subscription, it is recommended you unsubscribe before deleting your account or the app.
How to delete Tachyon VPN account:
Generally, here are your options if you need your account deleted:
Option 1: Reach out to Tachyon VPN via Justuseapp. Get all Contact details →
Option 2: Visit the Tachyon VPN website directly Here →
Option 3: Contact Tachyon VPN Support/ Customer Service:
- Verified email
- Contact e-Mail: [email protected]
- 100% Contact Match
- Developer: BLOCKSTONE LTD
- E-Mail: [email protected]
- Website: Visit Tachyon VPN Website
Option 4: Check Tachyon VPN's Privacy/TOS/Support channels below for their Data-deletion/request policy then contact them:
- https://tachyon.eco/?n=yr8mtzfwee.PrivacyPolicy
- https://tachyon.eco/?n=yr8mtzfwee.TermsOfUse
- https://twitter.com/tachyon_eco
- https://t.me/tachyoneco
*Pro-tip: Once you visit any of the links above, Use your browser "Find on page" to find "@". It immediately shows the neccessary emails.
How to Delete Tachyon VPN - Private Proxy from your iPhone or Android.
Delete Tachyon VPN - Private Proxy from iPhone.
To delete Tachyon VPN from your iPhone, Follow these steps:
- On your homescreen, Tap and hold Tachyon VPN - Private Proxy until it starts shaking.
- Once it starts to shake, you'll see an X Mark at the top of the app icon.
- Click on that X to delete the Tachyon VPN - Private Proxy app from your phone.
Method 2:
Go to Settings and click on General then click on "iPhone Storage". You will then scroll down to see the list of all the apps installed on your iPhone. Tap on the app you want to uninstall and delete the app.
For iOS 11 and above:
Go into your Settings and click on "General" and then click on iPhone Storage. You will see the option "Offload Unused Apps". Right next to it is the "Enable" option. Click on the "Enable" option and this will offload the apps that you don't use.
Delete Tachyon VPN - Private Proxy from Android
- First open the Google Play app, then press the hamburger menu icon on the top left corner.
- After doing these, go to "My Apps and Games" option, then go to the "Installed" option.
- You'll see a list of all your installed apps on your phone.
- Now choose Tachyon VPN - Private Proxy, then click on "uninstall".
- Also you can specifically search for the app you want to uninstall by searching for that app in the search bar then select and uninstall.
Have a Problem with Tachyon VPN - Private Proxy? Report Issue
Leave a comment:
What is Tachyon VPN - Private Proxy?
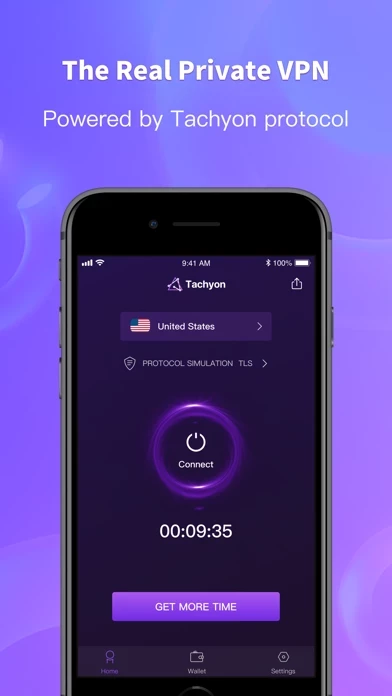
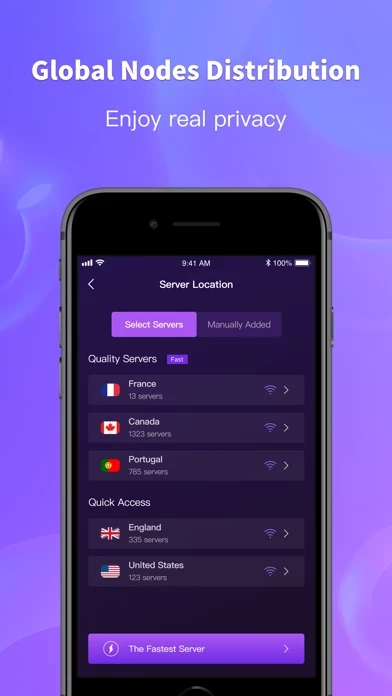
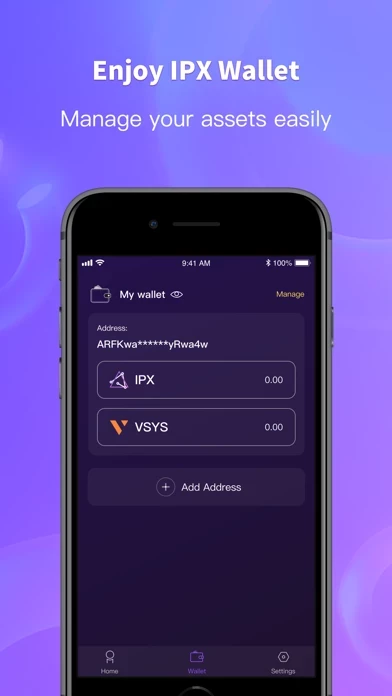
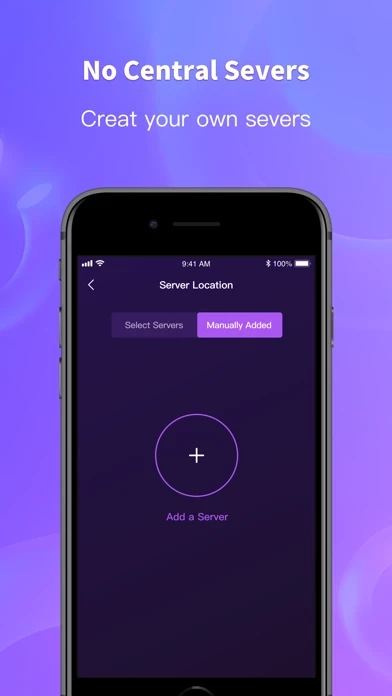
Download and try Tachyon VPN which is driven by all global users and powered by the unique Tachyon Protocol! Surf the internet with full privacy! We also offer the wallet service inside Tachyon VPN so that you can manage your IPX and other assets easily. > No Central Servers! Tachyon VPN functions as a platform instead of a central service provider. All servers you use will come from other global users which are distributed around the world and operated by different people. Since there is no central server to relay information, there is no possibility of data-logging in a single repository, which means no one can collect your privacy and sell your personal information when central servers are removed. > Conceal Your Data Perfectly With Unique Protocol Simulation Scheme! This scheme guarantees that the real content of the communication is concealed, in order to avoid information unwarranted interception and exposure. It also fools the third party applications into letting users’ da...